SMS firewalls are essential tools to securing a mobile operator’s network and revenues. However, with fraud constantly evolving, so should your network protections efforts. In this article, we look at five best practices that will help you stay at the top of your firewall game.
Clear traffic segregation
Separating P2P from A2P is a key function of a firewall. Firewalls don’t just protect against spam or malicious messages; they also aid in monetising messaging. But there is some simple housekeeping that can be done to aid and enhance this process.
Segmenting and identifying messages by source allows the firewall to quickly identify traffic coming in over certain grey routes.
Additionally, it is vital to understand the different potentials of local and international traffic. International traffic has a greater value than local traffic because of the commercial relationships its transit is built upon and the network resources it uses, not to mention its utility to the enterprise — hence it should be priced higher than local traffic.
Without distinct traffic segregation, a mobile operator will never receive the full value of their messaging traffic since a significant portion of it might be priced at a considerably lower rate, being mistaken for local traffic. However, even when operators do make this distinction, the traffic still may not be divided into clear, unambiguous “streams.”
At its most basic, traffic segregation can be achieved by controlling the connection types each kind of traffic has access to. This way, you can separate traffic into clearly defined types based on the protocol used, which potentially means tracking traffic origins and potential manipulations by analysing the data.
The final thing to consider is that separating international SMS from domestic requires learning which is which. Since you can’t just rely on global titles or IP addresses to reliably tell the traffic’s origin, you first need to associate these identifiers with a certain service, figure out where it is based and where this service sends its messages from. This brings us to…
Thorough testing
An exhaustive testing regime reveals network vulnerabilities, which is vital at the start of a monetisation project when few rigorous rules will be in place. Continuous testing provides an even better picture of evolving threats, showing you any changes in traffic trends.
Manipulating sender IDs, exploiting under-protected P2P connections, or SIM farms — everything goes for the dishonest players looking for ways to bypass your firewall and increase their margins.
For this reason, a wide-ranging database of international services and manipulations allows prioritisation of services most relevant to the operator’s business.
Using a database of prominent international services and unique message details associated with each helps to combat such manipulations, making it easier to spot deviations in the message contents and global titles, revealing the likelihood of noncompliant routing. Combined with the operator’s own insights and considering their priorities, this helps to fine-tune the operator’s SMS firewall. With threats constantly evolving, a programme of ongoing testing and reporting becomes vital for monetisation efforts.
Setting the right SMS Firewall ruleset and ongoing firewall management
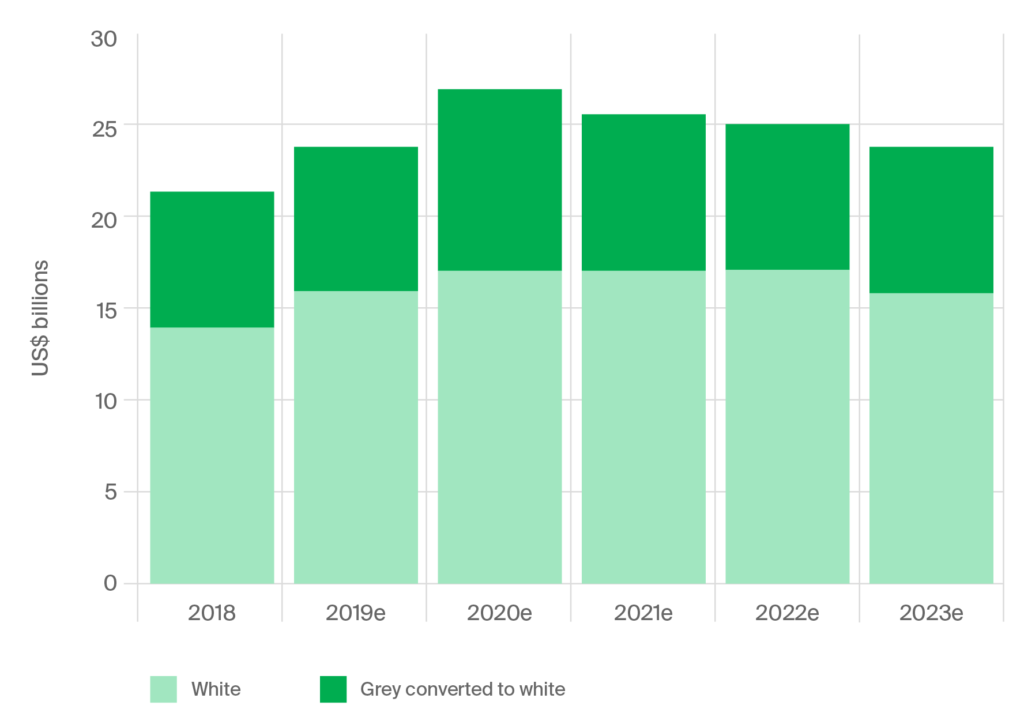
Things can become quite chaotic when traffic reaches the firewall — with all the numerous exploits like notorious grey routes and the sheer complexity of messaging routing. Hence, one of the firewall’s roles is to organise all incoming traffic via an effective set of rules.
We have already made the first steps by sorting the traffic into A2P, P2P, and P2A and cross-categorising it into national and international. The next obvious step is sifting out spam. Finally, it is necessary to come up with the blocking rules for illegitimate traffic, which can be a tad trickier: you have to be aware of the bypass techniques and manipulations used by fraudsters, which can vary from market to market.
It is worth notice that simply deploying a firewall is not enough for sufficient network protection. Eliminating SMS grey routes and dealing with unbillable messaging for good calls for proper firewall configuration. This means continuous rules updates and reconfiguration as new threats arrive. With fraudsters constantly looking for new exploits and unprotected routes, firewalls must be maintained and rules updated just as frequently.
Securing the revenues with machine learning
Machine learning is all about looking for patterns, which means that a properly trained machine learning system can be instrumental for detecting fraud travelling through the network.
Instead of manually managing IDs, blacklists and whitelists, an adequately trained machine can recognise patterns in message content and sort messages into categories, such as international/domestic, P2P, A2P, P2A, spam, etc. In such cases, fraud and spam are treated as another class of messages, which the firewall can then handle based on the previously established set of rules.
The other application of machine learning is grey-route reduction: a machine able of telling the difference between A2P and P2P, and determining the traffic origins, can facilitate proper traffic routing, ensuring proper messaging termination and protecting the operator’s revenue.
Finally, since the system can learn, adapting as traffic patterns change, it allows the firewall to evolve with the threat. As it learns about the network, the machine gets a better understanding of the nature and origins of the messages passing through it to accurately identify even the messages’ incomplete metadata or altered contents.
Going beyond — ZeroTrust
Another threat to the MNOs reputation and revenues is malicious software and SMS phishing. Usually, the culprits prompt the victim to compromise their sensitive data by clicking a link, calling a phone number, or contacting an email address provided via SMS message and sharing their details. More advanced menaces like the recent FluBot can combine smishing with trojan malware, which means that no data stored on the infected device is safe, making possible repercussions almost catastrophic.
While SMS firewalls are instrumental for identifying and blocking spam and number spoofing, even the best firewalls cannot automatically verify the security of a URL contained in the message. Since the real threat is the hyperlink itself, the firewall’s rules must be updated and managed constantly. The obvious solution would be blocking all messages that contain known malicious URLs. Such hyperlinks are usually registered on the same day of the attack and can either expire, be replaced or further altered down the line, which makes blacklisting these addresses ineffective.
Fortunately, it is possible to complement your firewall with advanced solutions like the Zero Trust approach, which only treats all hyperlinks as malicious unless proven safe, significantly decreasing the influence of a human factor, reliably protecting the subscriber data.
In conclusion
SMS firewalls are mobile operators’s trusty friends that help protect operator revenues and improve the health of the messaging ecosystem. Yet, optimising the firewall performance and bringing your network security to a new level calls for more than a simple firewall deployment. Contact our experts today to learn more about our solutions and ways to improve your firewall’s performance.