Unfortunately, the past few years have seen unprecedented volumes of fraud in the telecoms industry. But while the most discussed form of this fraud was smishing — a phishing attempt using SMS — mobile network operators (MNOs) were also hard hit by fraud. In 2019 the Communications Fraud Control Association published their biannual survey into fraud loss. It found that the telecoms industry lost $28.3 billion to fraud, with $2.71 billion lost to interconnect bypass types of fraud, which accounts for almost 10% of all lost revenue due to fraud.
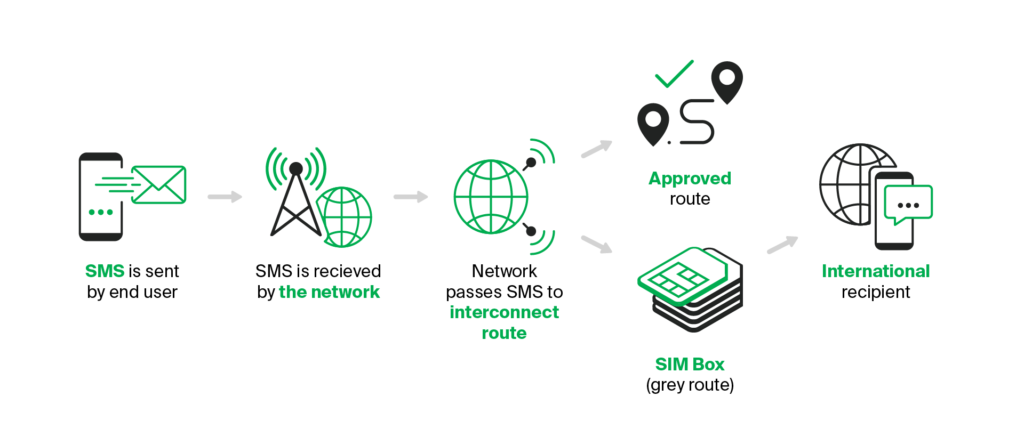
Interconnect bypass is based on international calling. Essentially, since international call charges are higher than national charges, fraudsters are using illegal methods to route international calls through VOIP and avoid international connection fees.
But what’s the motivation for the fraudsters? This isn’t a Robin Hood operation that is trying to get people lower call charges. Users pays the standard international call rate. When the fraudsters intercept the call, they route it using VOIP to make it seem like it’s a local call and then pocket the fee that the local network operator should have received.
The use of SIM boxes is the most common form of interconnect bypass fraud. This is a piece of hardware that has hundreds or maybe even thousands of prepaid SIM cards plugged into it, each one capable of rerouting a call. While they might only make pennies on the dollar per minute, this all stacks up when there are hundreds of calls in progress lasting multiple minutes at a time.
Combating SIM box fraud
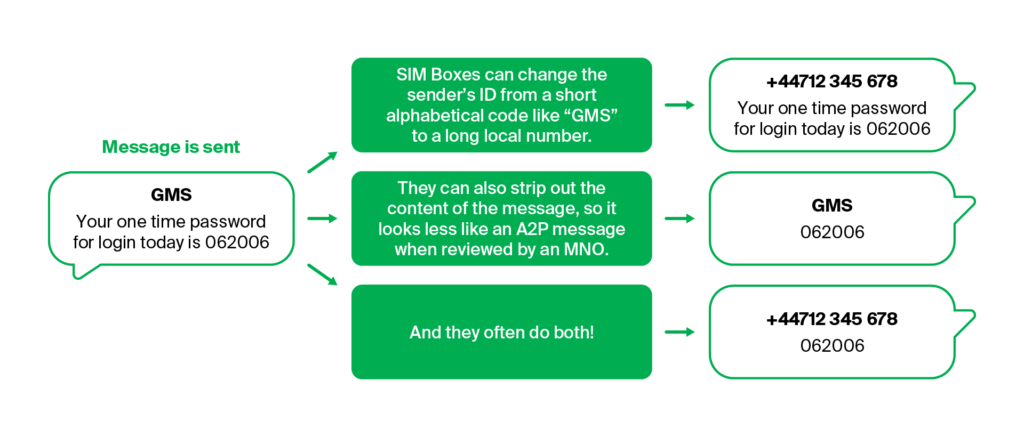
Fighting SIM Box fraud is a complex process, and there are multiple ways in which you can target fraudsters. One of the first things you need to do is stress test your network. You should use hardware local to your network to emulate the activity level of a large global enterprise, then simulate messaging traffic like one-time passwords for two-factor authentication and reminders. You can then check to see whether any factors of these messages were manipulated to sneak through grey routes.
Once you have these test results, you should analyse them. This will give you an indication of how much revenue you might be losing via all fraudulent traffic as SIM Box fraud and grey routes typically form a large part of that. This will also allow you to see the potential of your network. Once you know what’s being lost, you can work out the potential volume of a network. Most networks are not able to bring their network under control without support from a third party.
Taking control of your network
Your next step after testing is to start the process of taking control of your network. You’ll have your results and analysis, and the next step is another technical one — adjusting your firewall. SMS firewalls are built on a foundation of rules where messages with undesirable characteristics are blocked and the rest are sent to subscribers. You’ll need to update your firewall with new rules to stop the traffic that is sneaking past through grey routes via SIM boxes and other methods.
Unfortunately, with only being able to analyse just your traffic you’ll have to be reactive to what you receive and are able to identify. For the best possible outcome when working with your firewall rules you’ll probably want to work with a partner company like GMS. We work with a lot of networks all around the globe, actively monitor emerging trends and techniques, and can help you block them off on your network proactively.
However, you cannot just make technical fixes. You should also work with your legal teams to help shore up your contracts to prevent abuse by unscrupulous partners, working in contractual elements like fair usage policies to prevent abuse of your service.
Finally, you need to also look at your product offering from a fraudster’s perspective. How might your pricing model be updated to make it less attractive for them to defraud you? For example, you could limit the usage of SMS bundles to P2P traffic and clearly specify the allowed volumes. Work with your commercial team to fine tune your product offering so that it is set up to be more fraud resistant.

Head of A2P Division at GMS
To grow your network, you need to take control of your network. It is critical to have clarity on what is happening in your network, what services are using the network, what users are doing and how to differentiate between local and international traffic. By working with a global network of partners, GMS has a comprehensive understanding of what is happening both in your market and around the world.
A long-term partnership
You can do a lot of the above steps yourself, to a degree, but as mentioned in the section on firewall updates many networks will benefit from working with a partner with a wider knowledge base than themselves.
You might be looking at this and thinking that it looks like a long and in-depth process, and you’d be right. Our partnerships are all designed to be long-term working relationships. We monitor our partner networks 24/7 — 365 days a year to help them protect their traffic and their revenues.
While this is a long-term process you will likely see some incremental improvements in the early phases. Some of the changes, like introducing new firewall rules, can have effects soon after implementation, and our analysis will help MNOs fully understand their networks. Better knowledge of your network, the traffic going through it, and how to monetise it is essential for growing future revenues.
GMS has the expertise to provide MNOs with the support they need to realise the potential of their network. If you’d like to hear further information on how we do this and what we can do to grow your revenue, speak to one of our experts today.

